IT & Engineering
3 secure email gateway holes you need to close
Whether you’re working from home or rejoicing in the return to your spinny desk chair, one thing is certain: email lives on. Even as we move past the pandemic, email channels are playing an important role as the key tools to facilitate corporate communication. That’s why it should come as no surprise that threat actors use email to deliver malware in nearly every case of a reported cyber-attack: 94% of cases, to be precise. Organizations that rely on constant email communications need a security solution that prevents their email channel from becoming a vulnerable attack vector. This is where email gateways come in.
What does an email gateway do?
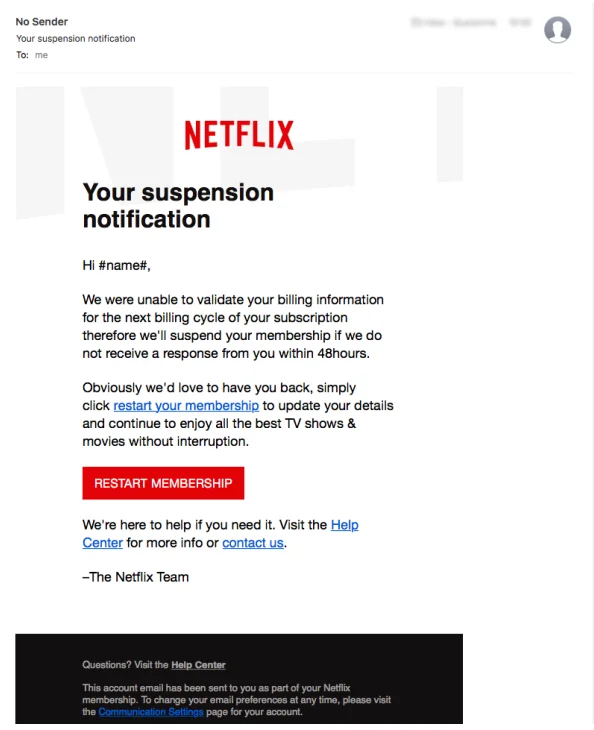
Sadly, an email gateway has nothing to do with Bill Gates, Stargates, or certain types of recreational substances – but they’ve got their own advantages. The most reliable and sophisticated security solution for any email channel is a secure email gateway, which can work for enterprises both large and small. Secure email gateways halt bad content – such as phishing emails that spoof legitimate businesses – in their tracks before they can ask you or a team member to input personal data like your login credentials or social security number.
These secure gateways aren’t foolproof solutions, though – other threats that regularly target inboxes often get around secure email gateways by exploiting disadvantages.
It’s important that organizations arm themselves against emails containing spam, phishing, malware, and other fraudulent content in a largely remote world. To get the ball rolling, let’s take a quick look at the top three secure email gateway holes that need to be closed as soon as possible and what you can do to keep your email channel protected.
Email gateway hole #1: Undisclosed malware signatures
Secure email gateway tools have done their best over the years to keep up with rapidly evolving malicious programs. Unfortunately, previously unknown threats multiply on a daily basis, and many are unlikely to be found in your gateway’s database of recognized and disclosed malware signatures.
Threats with undisclosed malware signatures are especially dangerous to enterprises, especially considering that 80% of successful breaches use signatures that are undetectable by traditional signature-based email gateways tools. So… not great.

Zero-day threats with undisclosed malware signatures are so problematic because they outpace the dynamic threat intelligence methods that even the most modern secure email gateways use. Once these threats get ahead of these threat feeds, they’re able to get the binary stamp of approval and move forward through the rest of your email channel. After threat actors have compromised your email channel, they can infect or compromise other sensitive data that would have otherwise been inaccessible to them. So… really not great.
Your organization must constantly be learning from the threats of the past in order to be prepared for the cyber threats of the future. According to cybersecurity expert Barbara Ericson of Cloud Defense, “by identifying, assessing, treating, and reporting on existing vulnerabilities in your email channel using a vulnerability management solution, you’ll enjoy greater digital security across the board and experience fewer intrusions or cyberattacks in the long run.” So… pretty good, actually.
Keep in mind that you and your IT team may need to perform further analysis on gathered data to identify patterns in vulnerabilities across your email channel and to anticipate future problems before they arrive.
At the end of the day, phishing and ransomware vulnerabilities are primarily driven by bad digital hygiene, like employees clicking on unfamiliar emails while logged into their work accounts or failing to run good antivirus software. Always account for these scenarios while using quality vulnerability management software that’s part of your organization’s greater digital security framework and strategic philosophy.
Email gateway hole #2: Phishing that uses multiple components
Secure email gateways have traditionally specialized in protection against straightforward ransomware and malware attacks. “Straightforward” attacks can be better understood as cyber assaults that rely on a single stage of an attack using a limited number of malicious components and modules.
Multi-stage assaults, on the other hand, use techniques to obscure malicious payloads that hide within user applications after they deploy from an unwittingly opened phishing email.
There are already plenty of reasons to be hyper-vigilant of scams, which have been rising significantly since the pandemic began. But sometimes even knowing how to detect a scam isn’t enough to adequately protect yourself from one.
In addition to using a secure email gateway tool, always remember to never share your personal or financial details, avoid clicking links and downloading files from unfamiliar sources, and use two-factor authentication to protect yourself from phishing attacks that use multiple components.
These considerations are particularly crucial to remember in light of the fact that a greater number of people and organizations are currently relying on email as their main means of remote communication between team members, clients, and vendors.
Multi-stage phishing attacks are most effective when they can deploy and disguise trojan payloads within a user’s applications. In the event that you access an email that you discover has been disguised by cybercriminals, a virtual private network (VPN) can add another barrier between threat actors and your personal information. Certain VPNs will mask your IP address and make it nearly impossible for cybercriminals to pinpoint your location and, consequently, the network you’re sending emails on.
VPNs, which are actually quite easy to install, can make it far more difficult for hackers to intercept data even after they’ve deployed a phishing email to your inbox. VPNs can also provide an even greater level of security by encrypting data that is sent between your phone’s inbox and a VPN server, even if the site you’re visiting doesn’t offer its own encryption.
Email gateway hole #3: Threats outside the body of an email
Phishing happens to nearly everyone, which is why most people tend to focus on the body of an email to spot phishers quickly. The body of an email typically has a few dead giveaways that make it easy for even non-tech savvy users to spot sloppy phishers and would-be data thieves. Most modern threat actors, though, are interested in email channels as an attack vector precisely because of outdated methods to spot phishers only inside the body of an email that so many people rely on.
Many secure email gateway tools have no way to identify nefarious payloads that embed themselves within a user’s hardware infrastructure or attachment applications. In other words, these secure email gateways are great at detecting threats inside the body of an email but have no way to spot threats disguised as elements such as macro programs or pixel data outside the email body.
But there is hope – organizations can combat these threats with solutions that scan for malicious content embedded within email attachments. Ensure that you invest in quality antivirus tools that are ready to deploy such as antivirus shields and firewalls, which can prevent viruses from compromising your machine by running regular precautionary scans. Without internet security and antivirus software, malware attacks can easily penetrate your network through sophisticated emails that evade your secure email gateway. When in doubt, stay safe!
Closing the gateway conversation
Secure email gateways are a great tool for email users, but they face challenges that they can’t overcome without the help of other resources. Organizations must acknowledge that their email gateways come with disadvantages and require other protections to close their vulnerability gaps and keep emails confidential and secure.
The biggest holes that secure email gateways must contend with include multi-stage phishing attacks, threats that deploy from outside the body of an email, and undisclosed malware signatures. Antivirus and vulnerability management tools, as well as proper cybersecurity hygiene like VPNs and two-factor authentication, can go a long way toward closing the holes that secure email gateways face in our working world. And, once you’re secure, you can go back to spinning happily in your spinny chair.
This post was written by Shanice Jones, a technical writer at shanicejones.com.