IT & Engineering
Vulnerability management: Working with the community to patch security threats
Cybersecurity is an endless struggle. The more you scale as a company, the more attractive you become to cybercriminals and the more challenging it gets to stay ahead of attacks. But cybercrimes are not exclusive to large organizations: according to a study, almost half (45%) of US companies have suffered a data breach in the past.
To prevent potential threats, companies need to adopt a holistic approach to cybersecurity and put the community at the core of their security efforts. Wondering how you can build a strong vulnerability management program and improve security across the board for your organization? Here are our tips.
Why is vulnerability management so important?
No matter how much we try, there’s just no way to guarantee an unhackable system. System failures, shifts in the tech space, and even human errors can expose even the most mature security programs, and ignoring the risks can have disastrous consequences for any company. System owners should always assume undiscovered critical vulnerabilities exist.
That’s why vulnerability management is a key aspect of any cybersecurity program. Vulnerability management programs allow companies to identify threats and blind spots in their products and infrastructure. They enable internal security teams to assess the risks and potential impact of these vulnerabilities so they can prioritize them and mitigate critical threats swiftly.
The faster a company grows, the bigger target it is for cybercriminals. A vulnerability management program prevents the increasing number of security threats from going undetected and protects the integrity of your application.
Building a mature vulnerability management program
You can’t protect your application and your infrastructure if you’re not staying one step ahead of external attackers. That’s the whole point of vulnerability management: to build a solid system for companies to anticipate and detect cyberattacks before they can harm their organization.
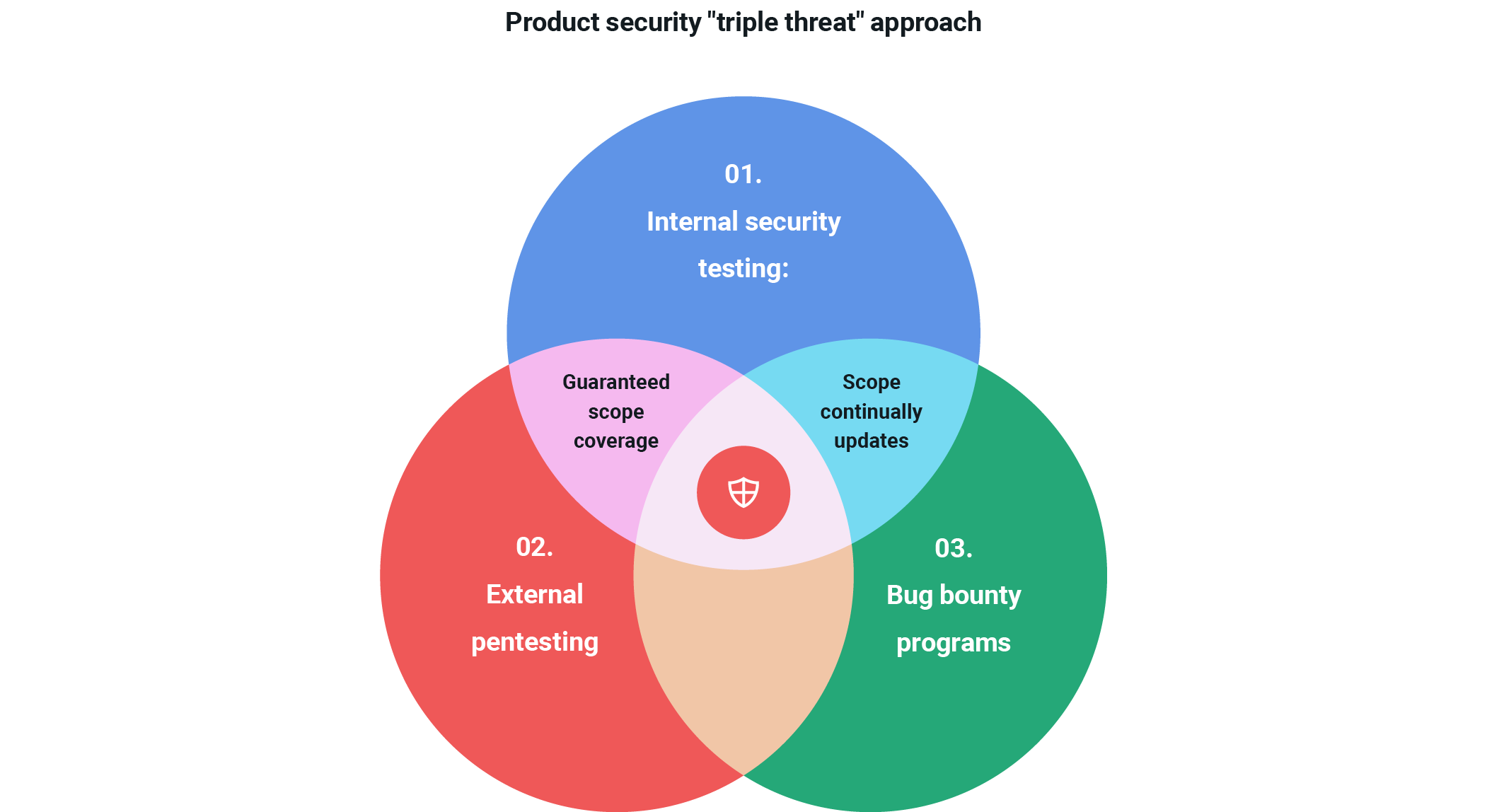
But with no magic crystal balls available, staying ahead at all times is easier said than done. Establishing a mature vulnerability management strategy requires a multifaceted approach that includes in-house experts for internal security testing, third-party firms for external pentesting, and bug bounty programs to attract community security researchers.
Working with the community to develop a stronger security posture
Constant technological shifts and system failures mean it’s impossible for internal security teams to anticipate and identify all potential security threats. Cyberattackers are getting more sophisticated, so engaging the community is the best way for organizations to be proactive in their approach to cybersecurity. Different hackers around the world have different perspectives and community researchers can bring that much-needed diversity to a company’s security program.
Bug bounty programs are an efficient way for organizations to scale their vulnerability management programs and bring unknown vulnerabilities out of the dark so they can be addressed. Through bug bounty programs, companies reward security researchers – or what some call “ethical hackers” – for finding vulnerabilities or security misconfigurations in their applications.
There are different approaches to bug bounty programs. They can be public and open to anyone, although many companies opt for private programs where they control who is invited to hack their products. Companies can also create their own rules for their bug bounty programs, so some might ask security researchers to focus on a particular product or service while others limit their bounty program to certain security issues.
Mailgun’s approach to vulnerability management
Security is key at Mailgun. We handle a lot of personal data, and keeping it safe is critical to our business. To offer the highest level of protection for our customer, Mailgun relies on a multifaceted vulnerability management strategy. Our three-pronged approach includes a strong internal security team that partners with our developers to test product security from planning to release, external pentesters that can quickly exploit system vulnerabilities, and a public bug bounty program that rewards security researchers for identifying and reporting on threats.
In the constantly evolving tech space, it really takes a village to keep our product and infrastructure secure, which is why the contributions of our bug bounty program are such an integral piece of our vulnerability management program. Our continuous and proactive engagement with the security researcher community has allowed us to identify bugs and vulnerabilities before they could be exploited by cybercriminals, something essential in order to keep our platform safe.
But it’s not just us – cybersecurity is all interconnected and sometimes other companies’ bug bounty programs can also help expose and mitigate misconfigurations in our own application.
Working with the community to patch security threats
This past summer, for example, one of our clients alerted us to a bug in our platform that was found by their customer’s bug bounty program. This particular issue could allow an account to bypass domain verification under specific circumstances. An account able to bypass verification could send DKIM signed messages that pass SPF verification for the newly created subdomain.
For that to happen, two conditions had to be met:
- A validated domain that is the target of the bypass needed to have an open/click tracking subdomain pointed to mailgun.org.
- The apex of a domain name that is the target of the bypass needed to not already exist on the platform.
While this bug would not have allowed the exfiltration of account or personal information stored on the platform, it would have enabled bad actors to send emails from our platform that would pass many DMARC policies in place to prevent spamming or phishing.
Thanks to the bug bounty hunter community and the work of our internal teams, we were able to swiftly address and mitigate this threat before it could be exploited by malicious actors. Mailgun customer accounts were not impacted or accessed in any way, and our team was able to carry out a full investigation to ensure our customers had not been directly targeted. The only attempts to exploit this vulnerability were tied directly to known security researchers.
Promoting the adoption of these bug bounty hunter programs across organizations and fostering a culture of collaboration when it comes to cybersecurity can help build a safer space for all.
Wrapping up
Vulnerability management is not easy, but establishing a solid cybersecurity foundation earlier on is the best way to ensure you’re protected against attacks. In the spirit of collaboration, here are our top tips for building a strong vulnerability management program for your organization:
- Run external and internal penetration testing regularly to identify potential threats before cybercriminals do.
- Build a team of security experts that can partner with your development teams to test your application before new releases.
- Enlist a third-party external pentest to perform a “point-in-time” test of your assets.
- Create a bug bounty program that invites security researchers from around the world to continually hack against your products. Start with a private program until you have established a good posture for handling the influx of reports.
At Pathwire, we’re eternally grateful for the security researcher community. The work they do enables us to stay ahead and offer the highest level of cybersecurity to our clients and, without them, Mailgun and Mailjet wouldn’t be the secure solutions you know and trust. So kudos to them for making the internet a safer space for all!
Find out why more than 100,000 customers work with Pathwire to build great apps and email programs.
