Deliverability
The BIMI email specification: Your reward for solid authentication

Remember in grade school when you’d get a gold star for a job well done? How about the feeling you get when you earn a new badge on GitHub?
It’s always cool to get recognized for quality work. And that’s really what the BIMI email specification is all about. When you’ve got your email authentication protocols nailed down and properly enforced, a BIMI logo is something mailbox providers like Gmail and Apple Mail may display as a bonus.
But before we dive into the technical details, let’s cover a few of the basics.
What is BIMI?
BIMI (pronounced bih-mee) is more than just a funny-sounding name. It stands for Brand Indicators for Message Identification. The simplest way to explain it is that, when you have all your email authentication ducks in a row, you’re eligible to be rewarded with your company’s logo showing up in the inbox.
Here’s a mockup from before and after BIMI setup:
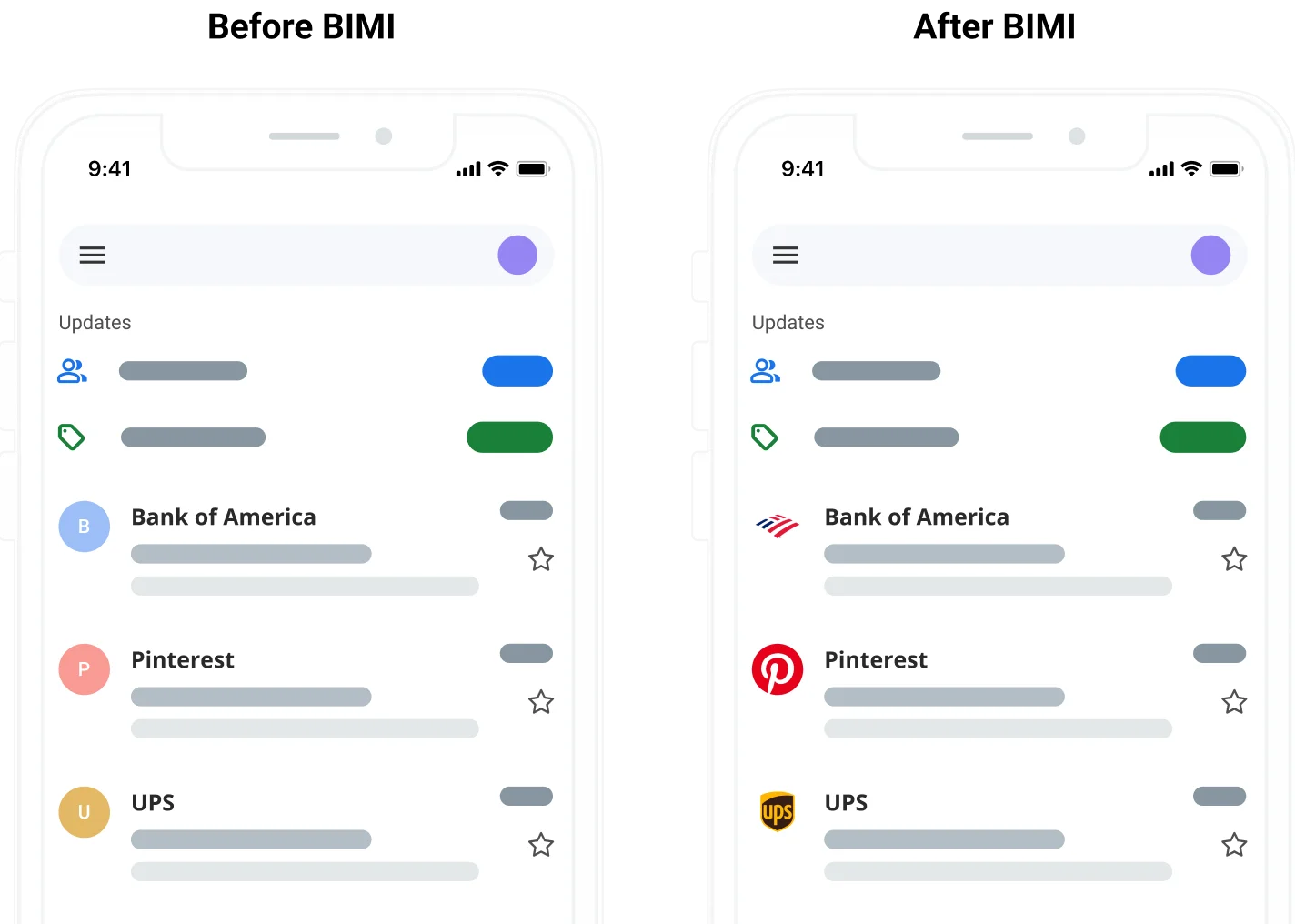
So, if someone asks you why your competitors have inbox logos and the company you work for has nothing but a letter inside a circle – this is most likely the reason why. You need to set up BIMI.
It’s not the first time we’ve seen inbox logos. Gmail tried doing it with Google+ profiles, and Microsoft Business Profiles made it possible in Outlook inboxes. But it can get messy. Mailbox providers often try to guess which logo is right, and inevitably, sometimes they’re wrong. Mailgun’s Chris Farmer explains some other ways that sender images show up in emails.
The BIMI method gives the sender/brand more control because they supply mailbox providers with an official, approved logo for inbox display.
Like other email specifications that are connected to the authentication process, BIMI is a DNS TXT record. When you have BIMI set up correctly, you should see your brand’s logo appearing in the inbox next to messages that you send.
But we’re getting way ahead of ourselves here. Before you can even start thinking about how to set up BIMI, we need to talk about DMARC.
The DMARC and BIMI connection
Domain-based Message Authentication Reporting and Conformance (DMARC) is one of the most important pieces in your email authentication puzzle. It’s currently the best way to stop scammers who want to spoof your brand using email. Unless you have DMARC set up with the right policy, mailbox providers will not show your BIMI logo.
As a quick refresher, DMARC is a specification that checks incoming messages for SPF (Sender Policy Framework), and DKIM (Domain-keys Identified Mail) alignment. Then, DMARC gives mailbox providers directions on what to do with email messages that fail authentication. This is known as your DMARC policy. For BIMI to work, your DMARC policy must be set to either quarantine or reject.
There are three DMARC policy options:
p=none– This policy doesn’t do much. It provides no direction concerning how to handle authentication failures, which leaves filtering decisions up to mailbox providers.p=quarantine– With this DMARC policy in place, you are suggesting that mailbox providers deliver authentication failures to the spam folder.p=reject– When this policy is in place, you are telling mailbox providers they should block or reject messages that fail authentication. It’s the strongest DMARC policy.
But here’s the problem… Most senders are only using the p=none DMARC policy. The purpose for the more relaxed policy is to maintain email deliverability while senders test DMARC and try to get it working correctly. It also allows for DMARC reports, which provide information on who’s sending mail on behalf of your domain. However, a p=none policy does nothing to help stop fraudulent email scams like phishing and brand spoofing.
BIMI implementation and DMARC adoption
While millions of senders are using DMARC, many aren’t taking advantage of its power to support email security. According to DMARC.org, nearly 66% of senders using DMARC still have a p=none policy. And that’s not exactly helpful to mailbox providers, or the recipients who are trying to identify and avoid email scams. It also means only 34% of senders using DMARC are even eligible for BIMI logos.
The website BIMIRadar.com tracks more than 67 million sending domains. As of this writing, it shows that just 2.2% of those domains are considered “BIMI-ready” and only a fraction of a percent has done everything required to implement BIMI correctly. So, this email specification has room to grow.
The main reason BIMI exists is to encourage senders to enforce stricter DMARC policies. Mailbox providers and others in the email industry created BIMI with what you might call a “carrot-on-a-stick” approach. They knew email marketers would want inbox logos, and BIMI would encourage senders to get serious about DMARC enforcement.
“BIMI is the carrot that Google’s using, that Yahoo’s using. They want people to adopt DMARC and get them to care about DMARC. DMARC makes their lives easier in terms of figuring out what mail potentially is legitimate and wanted.”

Of course, knowing how to set up BIMI for email typically falls on the shoulders of the IT department or others with more technical expertise. That’s because things can get a little complicated.
How to set up BIMI
As we mentioned, BIMI is a DNS TXT record that lives on your sending servers. Here’s an example of how a BIMI record might look:
default._bimi TXT "v=BIMI1; l=https://your-domain.com/your-logo.svg; a=https://www.your-domain.com/path-to-vmc/VMC.pem;"
That actually seems pretty simple, right? But remember, you also need to enforce a DMARC policy of either p=quarantine or p=reject for BIMI to work. In addition, the percentage of mail to which an enforced DMARC policy is applied must be 100. Here’s an example of a DMARC record that would be considered BIMI compliant.
v=DMARC1; p=quarantine; rua=mailto:dmarc-reports@example.com; pct=100; aspf=s; adkim=s;
You’ll notice that this DMARC policy is set to quarantine, and the percentage (pct=) is 100, which means the enforced policy applies to all mail. If this record included a sp=none tag, it would not be BIMI compliant. That’s because sp=none indicates there is a special policy of none for subdomains.
There are also some specific requirements for your BIMI logo:
- Senders must use an SVG file with the secure Tiny 1.2 format
- Your logo must have a verified mark certificate (VMC) from an approved entity.
In order to take full advantage of BIMI, senders need to obtain a VMC for a copyrighted logo from either DigiCert or Entrust, which are currently the only two approved organizations offering the certificates. The VMC requirement emerged when Gmail started supporting BIMI in 2021. More recently, BIMI gained support from Apple Mail (iOS 16 and Ventura 13), which also requires a certified digital logo.
If you’re a high-volume sender with multiple brands, there are ways to specify different logos for various brands and subdomains using what are known as BIMI selectors. This could also be helpful if you send transactional emails and promotional messages from different domains.
If you want to dig into the technical details even further, check out the BIMI RFC from the AuthIndicators Working Group.
BIMI setup in three steps
Now that you know the more common technicalities, let’s break down BIMI record setup step by step.
1. Confirm email authentication alignment
a. Is SPF set up and working?
b. Is DKIM set up and working?
c. Is your DMARC record configured correctly?
i. Is your policy set to quarantine or reject?
2. Create and verify your official, copyrighted logo
a. Use an SVG file in Tiny 1.2 format
b. Ensure the logo will display as expected when cropped for different inboxes
c. Obtain a VMC for your BIMI logo
3. Publish your DNS TXT record
a. Check for any typos in the TXT record
b. Make sure the DNS record points to the logo file location
c. Make sure it also points to your VMC file
It takes a week or two for a logo to start appearing in inboxes. However, you can use this tool from BIMIgroup.org to test your setup.
The benefits of a BIMI logo
So, why go through all the trouble of setting up and testing BIMI for email? Is an inbox logo really such a big deal, or is it just vanity? While the marketing team will love seeing a logo next to their campaigns, BIMI provides some other big benefits.
Brand awareness is definitely one of those benefits. Now that BIMI logos are supported in Gmail and Apple Mail, that covers a majority of the addresses on your list, especially for B2C organizations. BIMI is also available with Fastmail as well as Verizon Media Group’s Yahoo Mail and AOL.
An inbox logo is going to make your messages stand out from the rest of the crowded inbox, and it offers a more engaging user experience. That’s why higher email open rates are another potential benefit of BIMI. When Verizon Media trialed BIMI in Yahoo Mail, its results suggested that inbox logos could increase engagement by 10%. (Watch the video below for more.)
Yet another benefit is the subscriber trust factor. As your contacts and customers get used to seeing your BIMI logo, they’ll watch for it and notice when it’s not there. So, subscribers will know which emails to trust, and which are more likely to be spoofs from scammers. It’s a visual clue that an email is safe. That’s why many early adopters of BIMI are in the financial sector.
Email security and deliverability
Technically speaking, a BIMI logo does not make your emails more secure. And implementing the BIMI email specification won’t improve your email deliverability either – at least not directly. There is, however, a strong correlation between security, deliverability, and BIMI.
Because BIMI is proof that you’re doing your best to enforce strong email authentication, senders with BIMI are more likely to have a good reputation with mailbox providers. And a good sender reputation leads to better email deliverability. The same goes for BIMI and open rates. Senders with high subscriber engagement have a better reputation that supports deliverability.
DMARC and BIMI work together to protect your contacts from bad actors. BIMI itself doesn’t protect against phishing and brand spoofing. Logos can’t really do that. But DMARC does. When you enforce DMARC, you’re helping mailbox providers keep bad actors out of your subscribers’ inboxes. And since you can’t have a BIMI logo without a strong DMARC policy, that logo proves you take email security seriously.
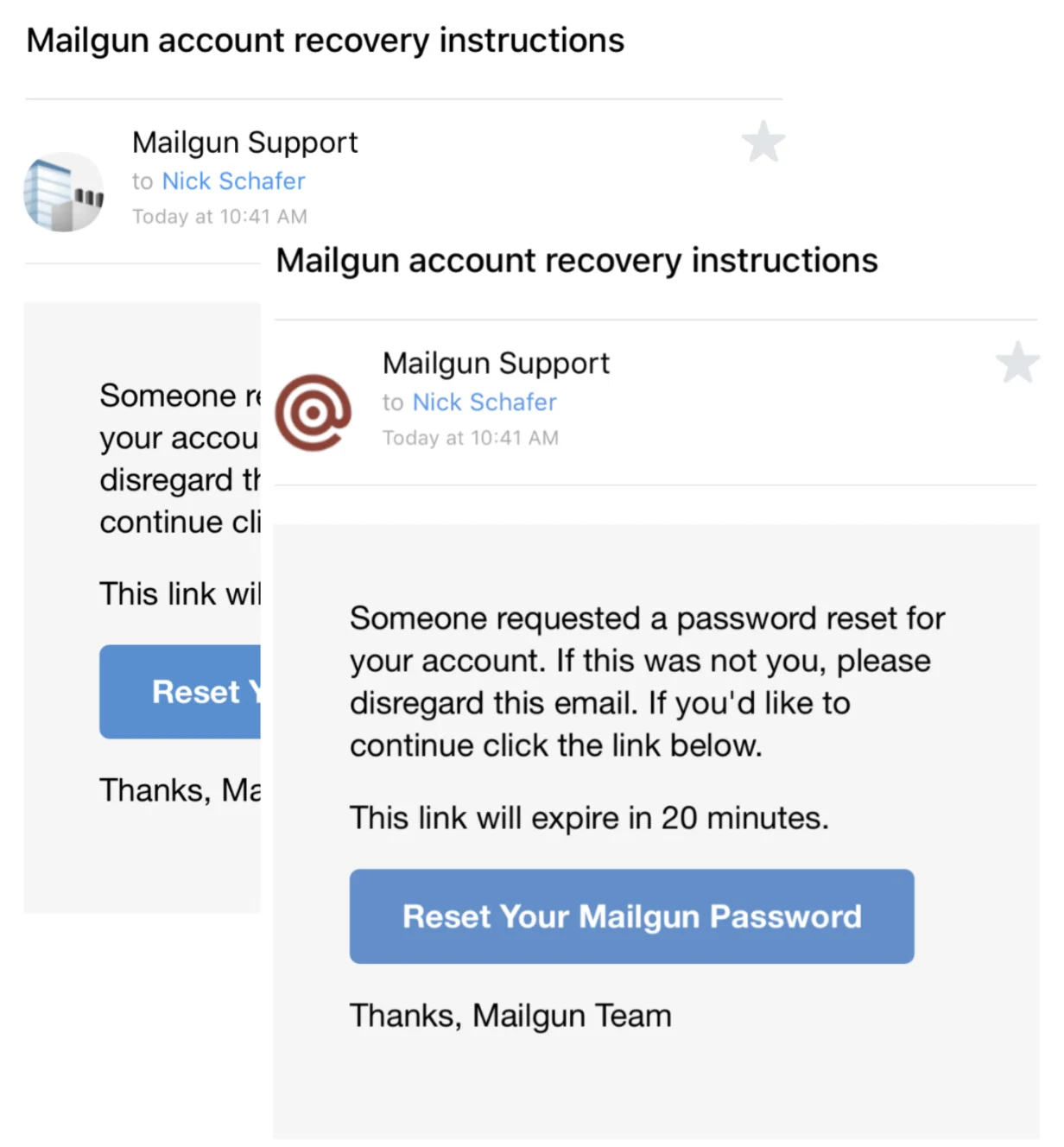
As a trust signal, a BIMI logo is very useful for important transactional emails. These are messages that are more likely to include sensitive information like account details or password reset instructions. Fake transactional emails are also a common phishing tactic, but seeing your BIMI logo means it’s safe to open the message.
How BIMI is evolving
If you’re in the email game, BIMI has been a conversation topic for awhile now, but we’re still in the early adoption phase. Basic authentication is now widely implemnted across domains, but even DMARC is still in its beginning stages. This is important, as we said, for a lot of inbox providers DMARC is the end goal and BIMI is what entices organizations to go through the certification process.
“Today BIMI is still in a bit of an early adopter phase where you actually will notice it in your inbox. If I’m looking at mail on my Gmail app on my iPhone, I see a logo and its the from avatar instead of initials or a blank avatar. That like stands out these days, which is one of the reasons why marketers should think about adopting. I think eventually it’ll be more of a cost of doing business potentially than it is now.”

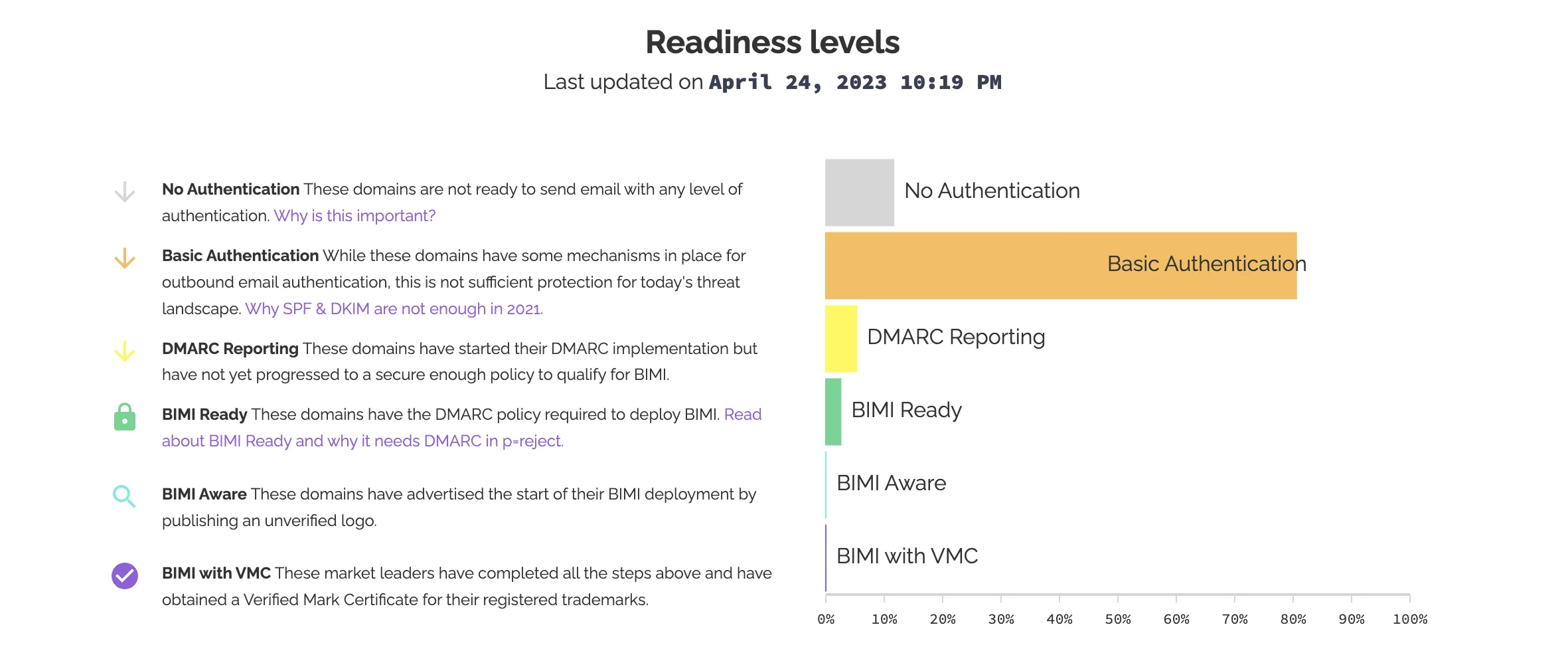
Readiness levels reported by Bimi Radar
Deliverability is more top of mind with marketers in 2023 and is becoming more widely adopted by inbox providers, some who have added on their own protocols. This is the 2023 landscape so far according to BIMI Group:
| Supports BIMI | Thinking about BIMI | No support |
|---|---|---|
| Cloudmark | At Mail | Microsoft |
| Fastmail | British Telecom | |
| Google | Comcast | |
| La Poste | Qualita | |
| Onet Poczta | Seznam | |
| Yahoo | Web.DE GMX | |
| Zone | Yahoo |
Google’s Verified Mark Certificate
In addition to BIMI, some providers are extended protocols even further – as with Google’s Verified Mark Certificate (VMC). The VMC is a digital certificate similar to BIMI, made specifically for Google’s platform. It requires that your company logo is a registered trademark and verifies that you are the legal brand owner.
Where VMC’s require proof of a registered trademark, BIMI is verification through DNS records. VMC’s are similar to BIMI in the sense that they build on it the same way DMARC is a prerequisite for obtaining BIMI.
Additionally, Google is adding more visual acknowledgmenet for BIMI to increase security for its users. Taking a note out of social media’s playbook, Gmail will start showing a checkmark icon for users that have adopted BIMI so their messages are easily distinguished between brand impersonators.
2023 updates from Brian Westnedge’s Email Camp session
Here’s the question, “do you think you can get additional engagement from having your logo next to your send address?”
It’s still early stages for BIMI, Google has been live with BIMI only since 2021 so there is not a lot of data but it’s safe to say that when logos are displayed in email campaigns, it leads to an increase in brand recall, open rates, and for retails an increase in purchase interest. Learn more directly from Brian Westnedge of Redsift as he talks through the industry questions and shares real world examples of how implementing BIMI and raising brand recognition leads to an increase in sender reputation and profit.
BIMI and Mailgun
At Sinch Mailgun, we require that every sender on our platform use SPF and DKIM authentication. If you don’t have authentication set up, we’ll do it for you. DMARC implementation is optional but highly recommended. We’re also big believers in using BIMI and can point our customers to the right experts who can help with DMARC and BIMI setup.
BIMI and DMARC aren’t the only ways to improve your security and sender reputation. Check out our in-depth guide for email security and compliance.