Product
Security matters: Say hello to two-factor authentication (2FA)
It’s that kind of Monday: You show up to work, and you’ve been logged out of your Mailgun account. You input your password, and it prompts you to enter a verification code sent via SMS to your phone.
Please input the six-digit code we sent to +1 (xxx) – xxx – 8318 to access your account.
Welcome to two-factor authentication, or 2FA for short. In this article, we’ll go over what 2FA is, different authentication factors, and types of 2FA. Then we’ll cover how to use two-factor authentication in your daily cybersecurity practices and what to do if you need help with 2FA.
What is two-factor authentication, and why do I need it?
2FA is a security system that requires two independent forms of identification to gain access to an account. This is useful for both account security and account recovery. Usually, the first form of security is your password to the account. The extra layer of security can rely on one of the following:
- A rotating, one-time password (OTP)
- A 6-digit authentication code
- A unique token
- A password or fingerprint confirmation via a second secure device (like a mobile device or a yubikey)
There are other methods, but these are the most common. The unique password or token is sent via email or text message to another trusted device, account, or phone number, and is required every time you attempt to log into your account. Anyone logging into your account will need to know your super-secret password AND access your 2FA code.
2FA increases the security of your account and guards against cybersecurity threats like phishing, key-logging, and other attacks by hackers. After all, you don’t want to send spam to your consumers after being hacked. 2FA is just as important for you as a developer as it is for your users.
According to an Insurance Information Institute report, consumers reported losing more than $3.3 billion to fraud in 2020. As cybersecurity threats become more prevalent, businesses are responsible for providing stringent account security for their websites and mobile apps.
What are different authentication factors?
2FA relies on two separate authentication factors to verify your identity and grant you access to your account.
Authentication factors are different categories of security credentials that can verify a user’s identity and authorize access to a secured account. The most reliable authentication factors are:
- Knowledge factor: This is an authentication credential based on the user having a specific piece of knowledge, like a password or personal identification number (PIN). Most generic (shared/multi-user account) logins use a username or email with a password or PIN to authenticate the user.
- Possession factor: This factor relies on the user possessing a device or way to access a piece of information, like a security key, to complete authentication procedures. For instance, in our example above, the user was instructed to input a six-digit code sent to a previously registered mobile device. This is an example of a possession factor, as the user must possess the registered phone to access the authentication code.
- Location factor: This authentication factor relies on geolocation through internet protocol (IP) addresses or media access control (MAC) addresses. Network administrators will use this to check the user’s location before allowing them access to a network, application, or system.
- Inherence factor: This relies on factors unique to the user, like biometric credentials such as fingerprints or facial recognition, to grant access. A mobile app may ask you to enter your username and password and then ask for a face ID or a fingerprint as a secondary form of authentication before granting you access.
- Time factor: This adds a time-based factor to authentication. For instance, a time factor can be a Time-based One-Time Password (TOTP) generated with a standardized algorithm and valid within a certain window of time. You’ll likely receive this via SMS or email.
What are the types of 2FA?
Now that we know the different authentication factors, let’s look at some types of 2FA which employ the above factors.
We’ll look at:
- Hardware tokens
- SMS verification codes
- Push notifications
- Software tokens
What are hardware tokens?
Hardware tokens are physical tokens, like a key fob or USB stick, that generate a new numeric code every 30 seconds or so. These tokens either display the code the user must manually input into their login page, or plug directly into a device’s USB port.
The downside to hardware tokens is that they’re easy to lose and are costly for businesses to replace.
What are SMS verification codes?
SMS codes are a common form of 2FA. The example at the beginning of this article is an example of an SMS verification code. Once the user tries to log into their account, they’re redirected to a second device where they receive a code to input on the login page to gain access to their account. In most cases, the primary device the user is logging in from is a laptop or desktop computer, and the second device is a mobile phone. Of course, there are variations on this if the user uses voice over internet protocol (VOIP) solutions like Google Voice.
What are push notifications?
Instead of sending the user a password or code, the website or application can simply send a push notification to an app notifying the user that a login attempt is happening. Then, the user can confirm or deny the login attempt to grant or restrict access.
What is a software token?
Software tokens, like TOTP, are one-time use, software-generated passcodes. First, the user must download and install a 2FA app on their computer, tablet, or smartphone. When they go to log into their account, they’ll be prompted to enter a software token generated on their 2FA app. These tokens are similar to hardware tokens in that they expire about every 30-60 seconds.
How do you use 2FA with Mailgun?
How you use 2FA differs depending on the web service. At Mailgun, our 2FA process requires the use of an authenticator app.
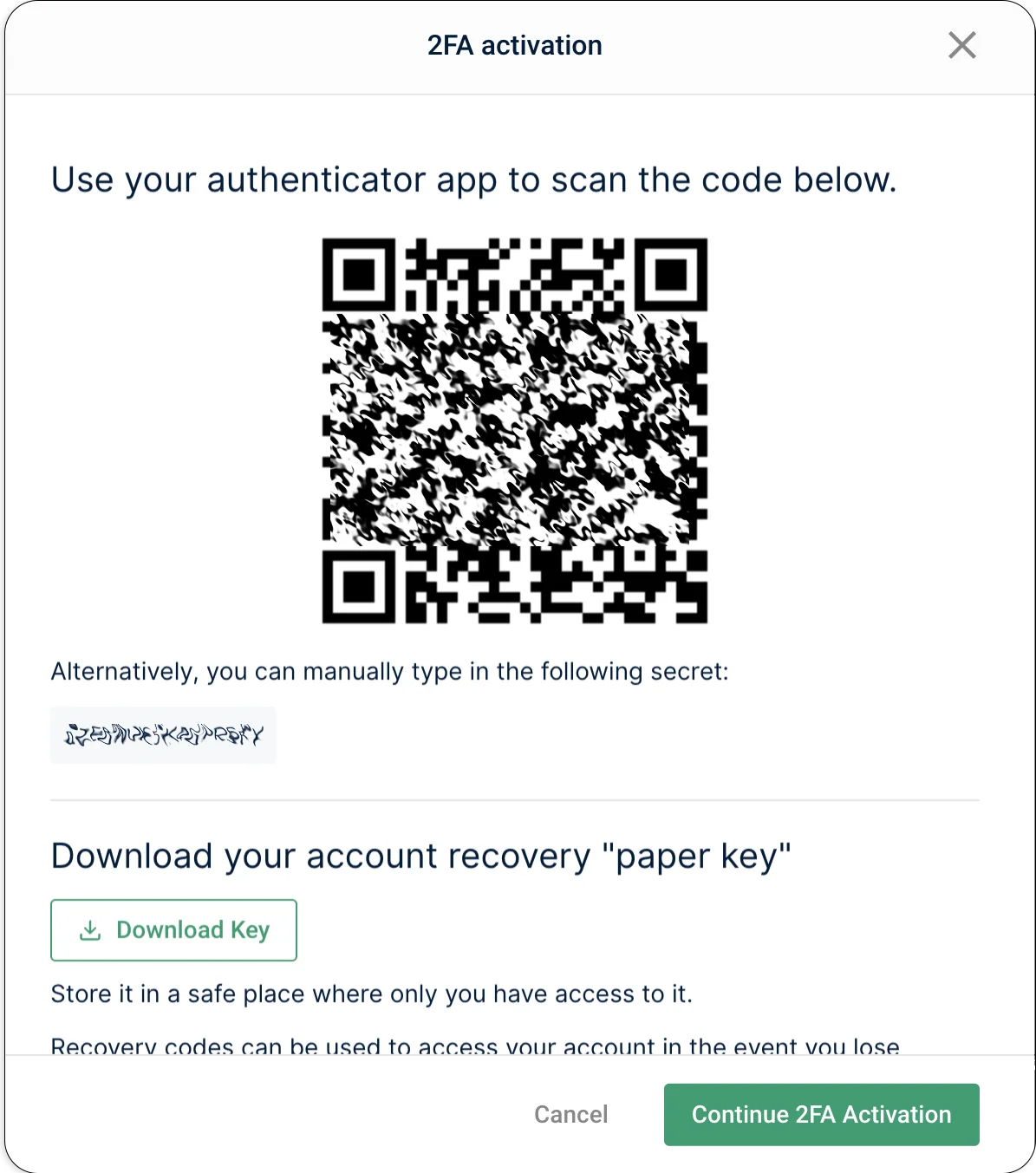
IMPORTANT: Before we dive into our 2FA process, we want to highlight the importance of step 5 below. When activating 2FA for your Mailgun account, you’ll see your account’s “paper key.” This key grants you access to the account if your authenticator app or device is no longer working. Keep this key safe – it’s shown only once and can’t be generated again. Not even our Mailgun team can retrieve your paper key for you.
Without further ado, here’s the process for using 2FA with your Mailgun account:
- Log into your Mailgun account.
- Click the dropdown menu in the top right next to your username icon.
- Select Security.
- Enable the 2FA option by clicking the Activate 2FA button, but do not close the window.
- IMPORTANT: Once you activate your 2FA, you’ll see your 64-character paper key. Click Download Key and store it in a secure location. We cannot retrieve this for you once you close this page.
- On this same page, you’ll see your secret key and QR code. You can retrieve these as needed.
- Install an authenticator app on your desktop or mobile device. Several applications will handle 2FA tokens for you. The most popular are Google Authenticator, Microsoft Authenticator, and LastPass Authenticator. These applications are typically installed on your smartphone and are supported on iOS, Android, and Windows.
- Add Mailgun to your list of services on your authenticator app. You’ll be prompted to scan a QR code or add a secret key to access your account.
What do I do if I need help with 2FA in Mailgun?
If you ever need help using 2FA with your Mailgun account, don’t hesitate to reach out to the Mailgun Support team. We’ll sort things out.
Keep in mind your paper key can help you authenticate if your app is no longer working.
Wrapping up
And that’s it! Use 2FA to keep your account extra secure. After all, your account is only as strong as your weakest access point. In fact, if you have a multi-user account with Mailgun, we recommend taking advantage of Mailgun’s user roles. On the off chance that your account ever gets compromised, this article can help.
Keep your keys close and out of prying eyes, your passwords complex, and your management team from firing you. Opt into 2FA to keep your accounts yours!
Is 2FA one of your security requirements? At Mailgun we stay on top of security and compliance standards. Learn more here about setting up an account and sending securely.
Want more security tips and email know-how? Don’t forget to subscribe to our newsletter so you never miss a beat.